In-time submission and academic quality guaranteed.
Cyber Security Essays
50 samples in this category
Essay examples
Essay topics
The issue of cyber security is not new but rather has developed for more than a half-century. Nowadays, cyber security has been a daily issue that can be found anywhere, from the news that reports spam, scams, frauds, and identity theft, to academic articles that discuss cyber warfare, cyber espionage,...
3 Pages
1593 Words
Trending 🔥
Cybersecurity has been growing rapidly since 2006 when cloud computing was introduced by most companies. Has a result more and more companies are spending more cash to improve their networks. There is no doubt that cyber has brought more problems with, however lack of training, unwarranted attacks, loss of property and human error have become a barrier that cannot be...
Why Cyber Security Is Important? Essay
2 Pages
1050 Words
Trending 🔥
Cyber security is known as the protection of computer systems from theft or damage to their hardware. It was developed in 1971 by a man named Bob Thomas. Cyberattacks happen daily, and they’re constantly evolving. The common cyberattacks that we hear about on the news are usually major data breaches or information leaks about our government. Simple viruses that started...
Cyber Security Essay
6 Pages
2749 Words
Trending 🔥
Introduction There are some processes and technologies that are formed for the security of computers, software, data, computer hardware and networks that are known as cybersecurity and all of these concerns things are protected by access and vulnerable supply via the Internet by cybercriminals, hackers and terrorist groups. The Internet and network that is based on information from unauthorized access...
The Importance of Cyber Security in Personal Life
5 Pages
2213 Words
Introduction Cyber security is a worldwide problem. We live in a highly connected and digital world. We will never be truly be safe from every cyberattack online but we can educate and protect ourselves. Ventures expects ransomware costs will rise to $11.5 billion in 2019 and expected to rise every year. Cybercrime affects national government, big business and average people....
SMEs Cyber Security Awareness
3 Pages
1647 Words
SMEs face a severe issue when it comes to cyber security, the issue faces all kinds of organizations, from big companies to small and medium enterprises. SMEs are usually targeted because of the less secure security protocols which makes them vulnerable to attacks that might lead them to close business or damage the business reputation. In the following research we...
Importance of Cyber Security Awareness in Information Technology
4 Pages
1850 Words
As the world keeps growing in technology, hackers are finding a new way to gain or access sensitive information. Lot of damage can be done using just a single device like your phone or laptop. Users nowadays needs to be aware of how a hacker tries to gain personal information which can be used against them to access their account...
Advantages of Cyber Security
2 Pages
892 Words
Introduction In the modern digital landscape, cyber security has become a cornerstone for maintaining the integrity and confidentiality of information systems. As businesses and individuals increasingly depend on digital platforms, the need for robust cyber security measures has gained paramount importance. Cyber security refers to the practices and technologies designed to protect networks, computers, and data from unauthorized access or...
Cyber Security
Essay on Cyber Security Roles
2 Pages
765 Words
The various topics learned in this course were quite insightful. Deception technology, as I have learned, gives an upper hand in cyber security to an organization. With the help of deception technology, corporations can be able to detect, in quick time, security risks and attempts by hackers to leak data, so the organization can terminate an ongoing cyber attack before...
Essay on Cyber Security Policy
2 Pages
938 Words
Introduction Avisitel is an international telecommunication US-based Company. In this project, the team will prepare a brief, itemized list of cyber-security policy issues as they apply to Avisitel. Premised on the list and the same industry-specific focus, a report about policies governing the different states as well as the federal government as a whole shall be reviewed taking into consideration...
Essay on Cyber Security Jobs
5 Pages
2090 Words
Introduction ‘There are only two types of companies: those that have been hacked, and those that will be.’ Robert Mueller I FBI Director I USA - March 2012 The ongoing demand for specialists in the Cyber community means there will always be options open to develop any computing career. Not only is cyber security becoming one of the fastest-growing economic...
Careers in Cyber Security
3 Pages
1212 Words
Introduction In today's increasingly interconnected world, the significance of cybersecurity cannot be overstated. With the rapid advancement of technology and the proliferation of digital devices, the threat landscape has evolved, making cybersecurity a critical priority for individuals, businesses, and governments alike. As cyber threats become more sophisticated and prevalent, the demand for skilled cybersecurity professionals continues to surge. This essay...
Essay on Is Cyber Security in Demand
2 Pages
965 Words
In less than a decade, the Internet has grown explosively which has drawn attention to billions of users and increased the number of online activities to an unprecedented rate. As a consequence, this led the whole world to a new digital age, where the majority of people nowadays are reliant on the Internet and technology for their needs. For Instance:...
How Does Cyber Security Conflicts with Freedom of Speech: Essay
1 Page
573 Words
Introduction: In the digital age, the emergence of cyber threats and the need for enhanced security measures have raised important questions about the potential conflicts between cyber security and the fundamental right to freedom of speech. While cyber security aims to protect individuals, organizations, and nations from online threats, the measures implemented to ensure security can sometimes encroach upon the...
Essay Speech on Cyber Security
1 Page
518 Words
Introduction: Ladies and gentlemen, Today, I stand before you to shed light on a matter of utmost significance in our modern society: cyber security. In an age where technology reigns supreme and our lives are increasingly interconnected through digital platforms, it is crucial that we understand the importance of protecting our digital assets, personal information, and overall cyber well-being. This...
Internet's Role in Cyber Security Issues
6 Pages
2910 Words
Urban infrastructure these days is not only about isolated nodes installed for the functioning of a community or society, but it is an interconnected realm of human interaction, deemed critical because of its impact on people’s lives and livelihoods. We have come a long way from when infrastructure was merely about roads, transportation, communication lines and other services that had...
Cyber CrimesCyber Security
Gap Analysis on Cyber Security: Essay
4 Pages
1818 Words
Executive Summary Equifax is a consumer credit reporting agency that gathers and aggregates data on millions of people worldwide in order to report on their credit. The company suffered a massive security breach in mid-2017 via vulnerabilities in the company’s digital infrastructure, causing the theft of a huge amount of personal data from the company. The Equifax breach was a...
Cyber CrimesCyber Security
Essay on Cyber Security in Indian Army
6 Pages
2859 Words
Introduction The ‘Stuxnet’ incident woke up the Indian cyber security setup from the abysmal slumber and self-induced sense of security & the discourse on critical information infrastructure (CII) protection in India was turned on its head. It was discovered that a large no. of hosts compromised by the Stuxnet attack were from India. The investigations that followed revealed the profound...
Cyber CrimesCyber Security
Cyber Security Threat Analysis Essay
4 Pages
2000 Words
Abstract Cyber security over the internet is the protection of internet-connected systems, including hardware, software, and data. Computer security or information technology security is the protection of computer systems from theft or damage to hardware, software, or electronic data, or unauthorized access. Cyber security is the practice of protecting systems, networks, and programs from digital attacks. Cyber securities are one...
Cyber CrimesCyber Security
Cyber Security Data Analysis Essay
3 Pages
1516 Words
Artificial intelligence for security Before examining the change in cybersecurity thanks to artificial intelligence systems, it is good to know some data. We are used to connecting artificial intelligence to computer programs such as voice assistants present in computers and mobile devices such as Cortana or Siri, as well as industry 4.0 linked to technologies that support humans in carrying...
Cyber CrimesCyber Security
Business Impact Analysis of Cyber Security: Essay
2 Pages
837 Words
According to DC. Latham an Assistant Secretary of DCCCI, “Over the past decade there has been an incredible growth in the amount of classified information stored in computers” (Warner, M., 2012). This data is stored in cyberspace which constitutes of many optic wires, routers, servers, and computers which are interconnected (Purpura, P., 2007). With the start of the 21st century,...
Cyber CrimesCyber Security
Air Force Speech on Cyber Security
5 Pages
2541 Words
Cyber Security an Invisible War The guard of our Nation has customarily been finished by using physical people as ground power. These ground powers push their way through foe lines to accomplish their destinations. As our reality changes and advances as new technology is presented, so do our ground powers. This is accepting structure as people keeping an eye on...
Cyber CrimesCyber Security
What Is the Cause of Cyber Security: Analytical Essay
2 Pages
956 Words
Cyber-attacks may not seem tangible in the digital world, but they can cause real damage. Technology and the internet join all countries together with the potential to be an asset or a weapon. A cyber-attack can reach a global level easily with low risk and the ability to cause damage on a high scale. Any nation that wants to cause...
Cyber CrimesCyber Security
Root Cause Analysis on Cyber Security: Analytical Essay
1 Page
484 Words
Cybercrime has become more prevalent in recent years. Discuss three different cybercrimes which were prevalent in 2018. When a crime is committed in the cyber world with the purpose to destroy, hacking the data system, or earning ransom is known as Cybercrime. For example: Network and data breach: It can be done via hacking a network system (Captures the data...
Cyber CrimesCyber Security
Persuasive Speech on Cyber Security
2 Pages
721 Words
The internet is a no man's land. The whole world has melted into a global village as the internet permeates offices, homes, and mobiles. Cyber security is the practice of protecting networks technological systems, and programs from data breaching, digital attacks, data infringement, and unauthorized access. These attacks mainly focus on accessing, changing, or in other words perishing important information,...
Cyber CrimesCyber Security
My Cyber Security Profession History Essay
1 Page
586 Words
I was the first among my friends and neighbors to get a computer around the age of 10. I can recall the glee and childish exuberance surrounding every aspect of my being on that morning my mother arrived from England. I was just elated seeing the Hewlett parked logo at boot up, then the black screen with white lettering long...
Cyber CrimesCyber Security
Log Analysis in Cyber Security: Analytical Essay
1 Page
555 Words
Log analysis is the term used by analyzers to analyze computer-generated records to help organizations or businesses mitigate different risks. Log analysis helps network engineers to manage different applications and infrastructures. Security analysts solve security problems. This process helps companies comply with security policies, audits, or regulations, and understand service troubleshooting. System and understand the behavior of online users. Website...
Cyber CrimesCyber Security
Cyber Security Thesis Statement Example
4 Pages
1718 Words
Executive Summary: Cyber security has its unique role in securing information in every sector. Protecting information from hackers has become more challenging. The first thing that strikes in mind with the word hacker is cyber threats which is a major concern for every data handling organization. Various policies and regulation acts were being implemented by organizations and governments to prevent...
Cyber Security Statement of Purpose
2 Pages
815 Words
In 2006, I graduated from the Kwame Nkrumah University of Science and Technology (KNUST) with a Bachelor`s degree in ElectronicElectrical Engineering. My interest in Cyber security was ignited in my third year at the University when we were introduced to TCPIP networking. In this course module, I learned how to use an Access control list and encrypted passwords to prevent...
Career ChoiceCyber Security
My College Goals in the Field of Cyber Security
1 Page
526 Words
“You know what’s better than building things up in your imagination? Building things up in real life.” I have experienced that the above quote has always worked for me. At a very young age as a student in high school, a computer for me was only a means of entertainment as I found it exciting to play games. I was...
College GoalsCyber Security
Why do You Want to Study Cyber Security
1 Page
621 Words
I humbly wish to further my educational career on the field of Cyber Security Engineering with TalTech Information Technology College. I sat down to look at our world from the past, present and visualize the future of information technology, how advance it has grown over the years. Everything in our day-to-day activities is computerize through the help of information technology,...
- 1
- 2
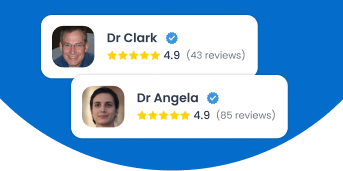
Join our 150k of happy users
- Get original paper written according to your instructions
- Save time for what matters most
Fair Use Policy
EduBirdie considers academic integrity to be the essential part of the learning process and does not support any violation of the academic standards. Should you have any questions regarding our Fair Use Policy or become aware of any violations, please do not hesitate to contact us via support@edubirdie.com.